How to Implement Audit Recommendations: Moving Beyond the Audit and Into Execution
I’ve watched teams pop the champagne after closing a grueling audit, only to feel the pit in their stomach return six months later when the exact same issue reappears in a follow-up review. It’s a specific kind of professional frustration: you thought you fixed it, but the fix didn’t stick.
The problem usually isn’t a lack of effort. It’s a breakdown in translation. We often treat audit reports as a checklist of tasks to be marked “done” rather than a signal of operational risk that needs a permanent process change.
If you are an operations lead, a controller, or a compliance manager in a growing business, you know the drill. You have a PDF full of “findings,” a leadership team asking when it will be clean, and a day job that didn’t go away just because the auditors arrived. Implementing recommendations isn’t just about making the auditor happy; it’s about operationalizing a fix so you never have to have that conversation again.
In this guide, I’m going to walk you through a structured, battle-tested workflow to turn those recommendations into action. We’ll move beyond vague promises and build a plan with clear owners, defensible evidence, and the kind of governance that keeps risks closed.
What I’ll cover (so you can scan and act)
- Triage & Prioritization: How to stop treating every finding as a fire drill.
- Root-Cause Reality: Why most fixes fail and how 5 Whys stops the cycle.
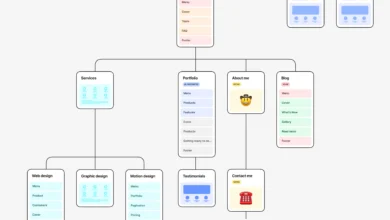
- The Translation Workflow: Turning audit-speak into a clear task list.
- Governance & Metrics: Dashboarding the follow-up so leadership stays informed.
- Continuous Assurance: Using AI and monitoring to stay audit-ready year-round.
Why audit recommendations stall (and what “successful implementation” actually looks like)

I used to think that a clearly written audit recommendation was self-executing. If the report said, “Segregate duties in accounts payable,” surely the finance manager would just… do it. But in the wild, recommendations stall because they collide with reality.
They stall because ownership is ambiguous (“I thought IT was doing that part”). They stall because the recommendation describes a perfect state, but your legacy system literally can’t support it without a six-month upgrade. And often, they stall because the business treats the audit report as the problem, rather than the underlying risk.
The landscape is shifting, though. Internal audit functions are moving away from purely checking boxes toward a strategic advisory role. In fact, Chief Audit Executives (CAEs) are aiming to increase their advisory activities to 40% of their workload . This means the expectation for implementation is higher. It’s no longer enough to say, “We updated the policy.” You have to prove the risk is managed.
The difference between closing an audit and closing the risk
Closing an audit finding is an administrative act. It involves sending an email or a screenshot to an auditor who marks a line item as “Closed.” Closing the risk is operational. It means the environment has changed so that the error cannot happen again without someone noticing.
Think of it this way: Updating a password policy document closes the audit finding. Configuring your domain controller to reject weak passwords and forcing a reset for all users closes the risk. The gap between those two is where repeat findings live.
A simple definition of “implemented” you can use with leadership

When you are reporting to your executive sponsor or audit committee, you need a definition of “done” that leaves no wiggle room. Here is the definition I use:
“A recommendation is implemented when the process change is executed, documented, tested for effectiveness, and assigned a continuous owner.”
To declare victory, check these boxes:
- Owner: A specific human (not a department) is accountable.
- Change Delivered: The configuration, process, or code is live.
- Tested: You have verified it works (don’t wait for the auditor).
- Documented: The “how-to” is written down.
- Monitored: There is a mechanism to flag if it breaks.
Turn each recommendation into an action plan (owners, scope, deadlines, and root cause)

The biggest mistake I see is copy-pasting the auditor’s recommendation directly into a project tracker. Auditor language is often formal and focused on the condition (what was wrong), not the solution (how to build it). Your job is to translate.
Start with risk and business impact (not the audit wording)
Before you assign a task, reframe the issue. Instead of saying, “We need to implement recommendation 3.1 regarding vendor onboarding,” say, “We are currently at risk of paying fraudulent vendors because our approval chain lacks a verification step.”
When you focus on the risk impact—financial loss, data breach, regulatory fine—you get buy-in. When you focus on “doing what the auditor said,” you get compliance fatigue.
Do a quick root-cause pass with 5 Whys

This is where you save yourself future pain. If a reconciliation was late, don’t just say, “We will be on time next month.” Ask why it was late.
Why? Because the data wasn’t ready. Why? Because the data export failed. Why? Because the script timed out. Why? Because the server creates a backup at the same time. Aha.
If you hadn’t asked those questions, you would have just yelled at the team to work faster. The real fix is rescheduling the backup, not “trying harder.” Root-cause methodologies are increasingly being used in audit follow-up because they stop the band-aid fixes that peel off in three months.
Table: Recommendation-to-implementation translation template
Here is a template you can copy into Excel or Google Sheets to manage this translation process.
| Audit Finding (Ref #) | Risk / Impact | Root Cause (The “Why”) | Remediation Tasks (The “How”) | Owner (RACI) | Test Method | Status |
|---|---|---|---|---|---|---|
| #3.1: Users have excessive access rights in ERP. | High: Potential for fraud or data theft. | Access is copied from previous employees during onboarding (“cloning”). | 1. Define roles by dept. 2. Remove “copy user” function. 3. Review current access list. |
IT Mgr (Accountable) HR (Consulted) |
Sample test of 10 recent hires. | In Progress |
| #4.2: Vendor contracts missing strict liability clauses. | Med: Legal exposure in case of breach. | Legal review happens via email, skipped when rushed. | 1. Implement mandatory workflow in procurement system. 2. Update contract templates. |
Legal Counsel | Walkthrough of system workflow constraints. | Not Started |
Step-by-step: how to implement audit recommendations in your business
Let’s get tactical. If you have a report on your desk right now, here is the workflow to get from “Open” to “Closed.” I’ll use a common scenario—an Access Control Finding (users didn’t lose access immediately upon termination)—to show how this works in practice.
Step 1: Confirm scope, constraints, and the real owner
First, stop the “everyone owns it” game. In the kickoff meeting, I always ask, “Who is the single person who will lose sleep if this isn’t fixed?”
For our Access Control finding, HR might say it’s IT’s job to click the button. IT might say it’s HR’s job to send the ticket. You need to lock the scope: Is this just for the ERP system, or all systems? Are we fixing the manual process, or buying an identity management tool?
Kickoff Checklist:
- Do we agree on the root cause?
- Do we have budget for a tool, or is this a process fix?
- Who is the ultimate Accountable owner?
Step 2: Prioritize recommendations with a simple risk-and-effort lens
You can’t fix everything at once. I’ve seen teams drown because they treated a typo in a policy document with the same urgency as a firewall vulnerability. Use a simple matrix:
- High Risk / Low Effort: Do these immediately (Quick Wins).
- High Risk / High Effort: Projectize these. These need a dedicated project manager.
- Low Risk / Low Effort: Batch these for a “cleanup day.”
- Low Risk / High Effort: Discuss with leadership. Should we accept this risk? (More on that later).
Step 3: Design the fix so it’s testable (control + process + evidence)

This is the most critical step. You must design a remediation that produces evidence naturally. If your fix requires someone to remember to take a screenshot manually every Friday, it will fail.
For our Access Control example:
- Bad Design: “HR will email IT faster.” (Hard to prove, prone to error).
- Good Design: “HR system automatically triggers a ticket to IT upon termination entry. IT must attach the closure log to the ticket before closing.” (System-generated evidence).
Step 4: Build the implementation plan (tasks, timeline, RACI)
Break the work down. Even a simple finding needs a plan.
- Responsible (R): System Administrator (configures the trigger).
- Accountable (A): IT Director (owns the risk).
- Consulted (C): HR Director (provides the data).
- Informed (I): Internal Audit (wants to know when it’s done).
Mini template: remediation status update
When you need to update stakeholders, keep it brief. Copy this:
Subject: Audit Remediation Update – [Project Name]
Executive Summary: We are currently [On Track / At Risk] to meet the [Date] deadline. Key configuration changes are complete and currently in testing.
- Completed this week: Automated ticket trigger configured in Jira.
- Blockers: Waiting for final sign-off on the new user termination policy from Legal.
- Next Steps: Run 5 sample test cases on Friday.
- Help Needed: Please approve the policy draft by EOD Thursday to keep schedule.
Step 5: Execute with change management (comms, training, enforcement)
Don’t underestimate the friction of change. When you roll out the new process, people will complain. They will say the new form is too long or the new approval step is annoying.
You need a rollout plan: Announce the change (“Why we are doing this”), Train the users (“How to do it”), and then—crucially—Enforce it. If someone emails IT directly instead of using the new ticket system, you have to gently redirect them. If you make exceptions early, the control dies.
Step 6: Test effectiveness (before you declare victory)
Never tell an auditor you are done until you have tested it yourself. Internal Audit will likely re-perform your test, so you should mirror their methods.
If I only have 30 minutes, I do a “Walkthrough.” I sit with the person doing the job and ask them to show me the new process live. I ask, “What happens if you click this? What if this field is empty?” You will catch 80% of the issues just by watching someone try to follow the new SOP.
Step 7: Document and package evidence for follow-up and re-audit
Future-you will thank present-you if you package the evidence now. Create a folder (or a link in your GRC tool) called “Evidence Bundle – Finding 3.1.” Inside, put the updated policy, the screenshots of the configuration, and the results of your self-test.
Writing clear, standardized documentation is often the bottleneck here. Whether you need to draft new Standard Operating Procedures (SOPs), create training summaries, or generate executive updates, using a specialized AI content writer can significantly speed up the creation of these artifacts, ensuring they are consistent and professional without eating up your entire week.
Build a structured follow-up process (metrics, reporting, and escalation)

Implementation doesn’t happen by magic; it happens by governance. You need a structured follow-up process that holds people to their promises. This isn’t about bureaucracy; it’s about visibility.
Who owns follow-up: internal audit vs management
Let’s draw a clear line. Management owns the remediation. Internal Audit owns the validation. Management should track their own progress in a central list or GRC tool. Audit should not be your project manager; if they are chasing you for updates every day, the process is broken.
Table: Follow-up dashboard metrics I recommend for beginners
You don’t need a complex BI dashboard. A simple spreadsheet tracked monthly works wonders. Here are the metrics that matter:
| Metric | How to Calculate | Why it Matters | Suggested Cadence |
|---|---|---|---|
| Overdue Aging | Days past original due date (0-30, 31-60, 60+). | Shows if issues are being ignored. | Monthly |
| Implementation Rate | % of items closed on time vs. total due. | Measures reliability of your promises. | Quarterly |
| High-Risk Open | Count of open findings rated “High” or “Critical.” | The “danger number” leadership cares about. | Monthly |
| Repeat Finding Rate | % of closed issues that reopen in subsequent audits. | Indicates poor root cause analysis. | Annually |
Escalation rules when risk is accepted (beyond appetite)
Sometimes, fixing a finding costs more than the risk itself. Or perhaps there is no budget this year. That is valid, but it must be a conscious decision, not accidental neglect.
If a High-Risk item is overdue by 60 days, or if a manager decides not to fix it, escalate it. Here is the script I use with the Audit Committee or Senior Leadership:
“We have assessed the recommendation regarding [Issue]. Implementing the full fix requires [$$$ or Resource]. Given our current priorities, we propose accepting this risk for [Duration], with the following mitigating controls in place to monitor it. Does this align with our risk appetite?”
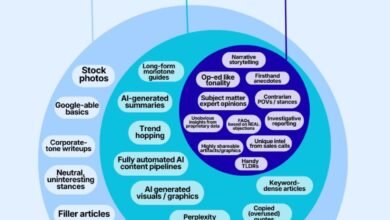
Use AI + continuous assurance to keep recommendations from reopening
The old way of auditing was “Periodic Assurance”—taking a snapshot once a year. The problem is that controls can break the day after the auditor leaves. The modern approach is “Continuous Assurance,” where you monitor data in near real-time.
Why continuous assurance beats “wait for the next audit”
Imagine a smoke detector versus a fire inspector who comes once a year. Continuous assurance is the smoke detector. By hooking into live data feeds, you can see if a control fails (e.g., a duplicate invoice is paid) immediately. This allows you to fix the process before it becomes a list of 50 audit findings at year-end.
Where AI helps most in implementation tracking (and where it doesn’t)
AI and intelligent automation are becoming huge assets here, but let’s be realistic about what they can do. I use automation for the “boring stuff” so I can focus on judgment.
What I automate first:
- Action Tracking: Automated emails that nag owners 7 days before a due date.
- Drafting Updates: Using Generative AI to summarize technical evidence into a clean paragraph for the executive report.
- Population Testing: Instead of testing 25 samples manually, scripts run against 100% of the transactions to flag anomalies.
The Limitation: AI cannot determine if a risk is “acceptable.” That requires human context. Trust the data, but verify the conclusion.
Common implementation mistakes (and how I fix them)
I’ve learned these the hard way. Here is a checklist of common pitfalls so you can avoid them.
Mistake-to-fix checklist (6–8 items)
- Mistake: Treating everything as Priority 1.
Fix: Force rank. If everything is urgent, nothing is. Focus on the High Risks first. - Mistake: The “email chain” fix.
Fix: Stop relying on “I emailed them.” Build controls into the system (workflow, required fields). - Mistake: Vague Due Dates.
Fix: Never accept “Q3” or “TBD.” Use specific dates (e.g., September 30th). - Mistake: Missing the “Evidence” column.
Fix: Define exactly what the proof looks like (file type and name) before starting the work. - Mistake: Single-threaded ownership.
Fix: If the owner leaves, the task dies. Always have a department head as a secondary owner. - Mistake: No testing before closure.
Fix: Implement a mandatory “self-test” step. You must break it before you mark it fixed.
FAQs + next steps (so you actually close the loop)
Let’s wrap this up with the questions I get asked most often when setting up these processes.
FAQ: Why is continuous assurance preferable to periodic audits?
Continuous assurance provides real-time visibility. Instead of waiting months to discover a control failure (and the associated risk exposure), monitoring detects issues as they happen, allowing for immediate correction and drastically reducing rework during the actual audit.
FAQ: How can AI support implementation of audit recommendations?
AI is excellent for acceleration and monitoring. It can automate the tracking of action plans, continuously test large datasets for compliance, flag overdue items, and even draft the initial reporting narratives. It reduces the manual administrative burden, letting you focus on solving the problem.
FAQ: What makes strategic alignment important for audit implementation?
When audit recommendations align with business goals, they get funded. Research shows that strategically aligned audit functions enjoy a significant funding advantage. If you frame your implementation as “helping the business grow safely” rather than “compliance homework,” you unlock budget and executive support.
FAQ: What should a structured follow-up process include?
At a minimum, it needs clear roles (Management owns execution, Audit owns validation), defined evaluation criteria (what counts as “done”), regular reporting to governance bodies (dashboarding metrics like aging and overdue counts), and a formal escalation protocol for risks that aren’t being addressed.
FAQ: How does root-cause analysis improve implementation outcomes?
It stops the cycle of repeat findings. By using tools like the 5 Whys to identify underlying causes—such as a lack of training or a broken handoff process—you implement fixes that address the source of the error, ensuring the issue doesn’t just pop up again under a different name.
3-bullet recap + my recommended next actions
Recap:
- Translation is key: Turn vague recommendations into specific tasks with clear evidence requirements.
- Governance drives execution: Use metrics and escalation to keep pressure on the system.
- Design for testing: If you can’t prove it with a system log or a report, the control isn’t strong enough.
Next Actions (This Week):
- Pick your top 5: Identify the 5 highest-risk open findings and run a quick “5 Whys” on them.
- Assign single owners: Verify every open item has one specific human attached to it.
- Set the cadence: Schedule a monthly 30-minute “Risk & Remediation” review with your leadership team.
- Create your evidence folder: Start building the “evidence bundle” for your next closure now, not the day the auditor arrives.
If you only do one thing, establish that monthly leadership review. Visibility is the best disinfectant for lingering audit issues.